Presentation by Brewster Kahle, Internet Archive Digital Librarian at Ford Foundation NetGain gathering, — a call from 5 top foundations to think big about prospects for our digital future. (More detailed version)
Hi, I’m Brewster Kahle, Founder of the Internet Archive. For 25 years we’ve been building this fabulous thing—the Web. I want to talk to you today about how can we Lock the Web Open.
 One of my heroes, Larry Lessig, famously said that “Code is Law.” The way we code the Web will determine the way we live online. So we need to bake our values into our code.
One of my heroes, Larry Lessig, famously said that “Code is Law.” The way we code the Web will determine the way we live online. So we need to bake our values into our code.
Freedom of expression needs to be baked into our code. Privacy should be baked into our code. Universal access to all knowledge. But right now, those values are not embedded in the Web.
 It turns out that the World Wide Web is very fragile. But it is huge. At the Internet Archive we collect 1 billion pages a week. We now know that Web pages only last about 100 days on average before they change or disappear. They blink on and off in their servers.
It turns out that the World Wide Web is very fragile. But it is huge. At the Internet Archive we collect 1 billion pages a week. We now know that Web pages only last about 100 days on average before they change or disappear. They blink on and off in their servers.
 And the Web is massively accessible, unless you live in China. The Chinese government has blocked the Internet Archive, the New York Times, and other sites from its citizens. And so do other countries every once in a while.
And the Web is massively accessible, unless you live in China. The Chinese government has blocked the Internet Archive, the New York Times, and other sites from its citizens. And so do other countries every once in a while.
 So the Web is not reliable— And the Web isn’t private. People, corporations, countries can spy on what you are reading. And they do. We now know that Wikileaks readers were targeted by the NSA and the UK’s equivalent. We, in the library world, know the value of reader privacy.
So the Web is not reliable— And the Web isn’t private. People, corporations, countries can spy on what you are reading. And they do. We now know that Wikileaks readers were targeted by the NSA and the UK’s equivalent. We, in the library world, know the value of reader privacy.
 But the Web is fun. We got one of the three things right. So we need a Web that is Reliable, Private but is still Fun. I believe it is time to take that next step. And It’s within our reach.
But the Web is fun. We got one of the three things right. So we need a Web that is Reliable, Private but is still Fun. I believe it is time to take that next step. And It’s within our reach.
Imagine “Distributed Web” sites that are as functional as Word Press blogs, Wikimedia sites, or even Facebook. But How?
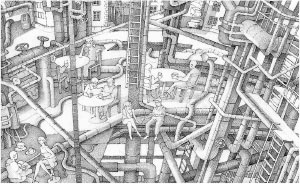 Contrast the current Web to the internet—the network of pipes that the World Wide Web sits on top of. The internet was designed so that if any one piece goes out, it will still function. The internet is a truly distributed system. What we need is a Next Generation Web; a truly distributed Web.
Contrast the current Web to the internet—the network of pipes that the World Wide Web sits on top of. The internet was designed so that if any one piece goes out, it will still function. The internet is a truly distributed system. What we need is a Next Generation Web; a truly distributed Web.
 Here’s a way of thinking about it: Take the Amazon Cloud. The Amazon Cloud works by distributing your data. Moving it from computer to computer—shifting machines in case things go down, getting it closer to users, and replicating it as it is used more. That’s a great idea. What if we could make the Next Generation Web work that, but across the entire internet, like an enormous Amazon Cloud?
Here’s a way of thinking about it: Take the Amazon Cloud. The Amazon Cloud works by distributing your data. Moving it from computer to computer—shifting machines in case things go down, getting it closer to users, and replicating it as it is used more. That’s a great idea. What if we could make the Next Generation Web work that, but across the entire internet, like an enormous Amazon Cloud?
In part, it would be based on Peer-to-peer technology—systems that aren’t dependent on a central host or the policies of one particular country. In peer-to-peer models, those who are using the distributed Web are also providing some of the bandwidth and storage to run it.
Instead of one web server per website we would have many. The more people or organizations that are involved in the distributed Web, the safer and faster it will become. The next generation Web also needs a distributed authentication system without centralized log-in and passwords. That’s where encryption comes in.
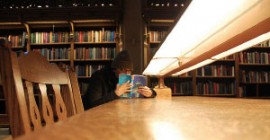 And it also needs to be Private—so no one knows what you are reading. The bits will be distributed—across the Net—so no one can track you from a central portal.
And it also needs to be Private—so no one knows what you are reading. The bits will be distributed—across the Net—so no one can track you from a central portal.
 And this time the Web should have a memory. We’d build in a form of versioning, so the Web is archived thru time. The Web would no longer exist in a land of the perpetual present.
And this time the Web should have a memory. We’d build in a form of versioning, so the Web is archived thru time. The Web would no longer exist in a land of the perpetual present.
Plus it still needs to be Fun—malleable enough spur the imaginations of a millions of inventors. How do we know that it can work? There have been many advances since the birth of the Web in 1992.
 We have computers that are 1000 times faster. We have JAVAScript that allows us to run sophisticated code in the browser. So now readers of the distributed web could help build it. Public key encryption is now legal, so we can use it for authentication and privacy. And we have Block Chain technology that enables the Bitcoin community to have a global database with no central point of control.
We have computers that are 1000 times faster. We have JAVAScript that allows us to run sophisticated code in the browser. So now readers of the distributed web could help build it. Public key encryption is now legal, so we can use it for authentication and privacy. And we have Block Chain technology that enables the Bitcoin community to have a global database with no central point of control.
 I’ve seen each of these pieces work independently, but never pulled together into a new Web. That is what I am challenging us to do.
I’ve seen each of these pieces work independently, but never pulled together into a new Web. That is what I am challenging us to do.
Funders, and leaders, and visionaries– This can be a Big Deal. And it’s not being done yet! By understanding where we are headed, we can pave the path.
 Larry Lessig’s equation was Code = Law. We could bake the First Amendment into the code of a next generation Web.
Larry Lessig’s equation was Code = Law. We could bake the First Amendment into the code of a next generation Web.
We can lock the web open.
Making openness irrevocable.
We can build this.
We can do it together.
Delivered February 11, 2015 at the Ford Foundation-hosted gathering: NetGain, Working Together for a Stronger Digital Society
July 2021: Title changed from “Distributed Web” to “Decentralized Web” as it came to be know that way.
I2P might be a basis for a decentralised, anonymous internet. (https://geti2p.net/de/)
Yacy can provide a p2p, decentralised search engine: http://www.yacy.net/de/
Blockchain could be used to verify all data transfers to guarantee that they are legitimate.
By the way, Archive.org has lots of servers and bandwith, why not running a few I2P/TOR non exit nodes ? This way archive.org could also crawl sites from the Darknet and add them to the wayback machine, making old TOR/I2P sites availible on the archive might be very usefull in case if they disapear on TOR.
Yes I have this running in my head also. A type of p2p I would say with a simple 2 step or 3 step verification for important operations. I also would say a cross checking system for the p2p, for the integrity of the data.
I Think we need to realize though this is a tremendous tool and that Ethics are lagging far behind this type of thing.
I would recommend whitelisting crawled eepsites and hidden services though, for obvious reasons.
Sooooooo…. Freenet? That thing that already exists?
Really, all it needs is a DNS and wider user base.
So where do we sign up?!
pretty much describing https://en.wikipedia.org/wiki/MaidSafe here
seems to me that maidsafe and bittorrent’s maelstrom and bitpay’s bitcoin-in-javascript and namecoin and … are all key steps in the right direction.
-brewster
RE: “Larry Lessig’s equation was Code = Law. ”
This formulation is not even false.
It commits the logical fallacy of equivocation by confusing two different kinds of things with the same appearance.
Computer code is prescriptive in that it tells a machine what it MUST do.
In contrast, legal code in a free society only tells an individual what they MUST NOT do, the actions to be avoided in order to keep the balancing action of the justice system from being put into motion against them.
Subsuming computer code and legal code under the same concept implicitly endorses fascism, which entails the use of the laws to dictate the actions of individuals.
Lastly, there is a conceptual error in use the “=” in place of “is” in “Code = Law”. Mathematical equivalence is not interchangeable with logical identity. This type of error blanks out the qualitative aspects of entities by using a quantitative linking term.
distributed Web sounds similar to distributed energy sources(DER) .a sort of convergence between computers & power!
http://www.correntewire.com/transcript_lawrence_lessig_on_aarons_laws_law_and_justice_in_a_digital_age
(Lessig discussing Aaron Swartz’s case)
Another aspect for decentralized net is the access. There are free wireless networks, which build up their own net with normal wifi-routers connected to antennas on the roof or in the window. Some also provide gateways to the Internet, but it can also be used as a local network for that area.
In Germany the “Freifunk” community recently had a successful court case which gave them the provider privilege. That means they as providers can not be held responsible for what their users do.
http://freifunk.net/en/
thankes your
I agree to most parts, but i am opposed to use javascript for this purpose.
In my opinion an informative website should be an static thing, consisting only of text, images, video, sound et cetera with the browser acting only as an agent that displays the contents.
If there is executable code – javascript for example – this opens the door for things that restrict freedom and privacy.
Freedom restriction because scripts can easily redefine the user interface, for example to disable the right mousebutton to prevent saving an image. Or even worse that content is available in encrypted form only and only decoded on the fly when viewing.
Privacy restriction because there are everywhere javascripts collecting informations about browsers, espically for Google Analytics. Some scripts even record in which way the user moves the mouse over an page.
Entertainment websites and online games are something different and may be as flashy as they want. I am only interestend in the informative part of the web.
Pingback: What we’re reading in February | Learn More